Advanced cyber threats continue to bypass the most sophisticated passive defenses. However, using an “active defense” approach with Deception-as-a-Service technology provides a real-time view of the attacker’s perspective and turbo-charges SOC performance, providing a powerful new tool to your organization’s cyber defenders.
Velaspan Active Cyber Engagement, powered by Acalvio’s industry-leading ShadowPlex capabilities, delivers a fully managed threat defense platform, providing early detection and real-time containment of sophisticated adversaries – backed up by Velaspan’s 24/7 expert SOC response support.
What is Deception Technology?
If a breach occurs, cyber deception answers the question: “What actions do we take when a breach is discovered.” The idea is to deliberately blanket an enterprise’s network infrastructure with “Deception elements” that are specifically designed to detect, direct, disrupt, confuse, and confound attackers. Proactively deploying these elements makes this an “Active Defense” approach, rather than responding to a breach with traditional tools.
Deception elements are not just decoys; they are special-purpose versions of the real thing. They trigger an alert only when accessed. Therefore, false positives are virtually non-existent because these elements exist outside of normal operational workflow. Any alert from Deception technology is worthy of inspection.
Active Cyber Engagement Improves the Protection of Your Most Critical Assets
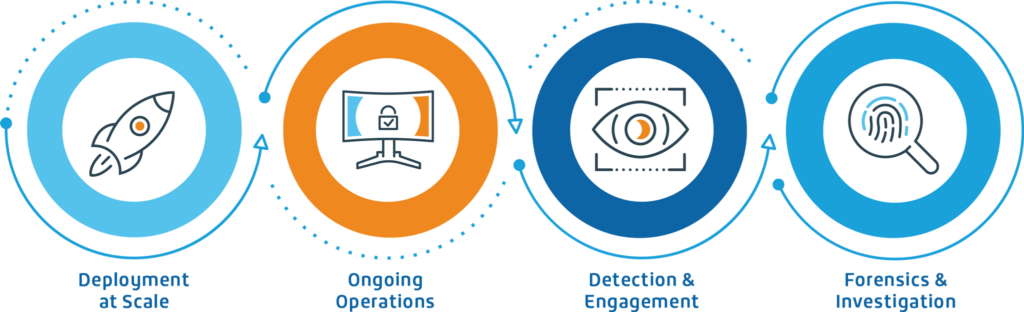
Fully Managed Service
- 24/7/365: Monitoring, Alerting, Containment, and Adversary Engagement
- Deception Security Operations Center (DSOC) Staffed by Senior-Level Analysts
- Integration and API support with Security Ecosystem (SIEM, EDR, Firewall,NAC, SOAR, etc.)
- Immediate Quarantine, Forensics, and Investigation by the DSOC
- Real-time online access to Dashboard Reporting and Threat Analytics
- Ongoing Periodic Threat HuntingEngagements
Benefits
- Reduced Attacker Dwell Time: Detection of malicious activity with Precision and Speed
- Rapid Investigation Capability including Active Threat Hunting
- Automated Response: Leveraging extensive integrations
- Minimal IT Overhead: Deception configured, deployed, and managed autonomously
- Low Total Cost of OwnershipCompared to Full-Time-Equivalent
Key Features of Velaspan’s Active Cyber Engagement Managed Services
Fully Managed Solution
- Platform alerts will be sent to the clients’ existing SOC tools as appropriate
- For clients without a SOC, the service provides a broad-based set of services which could be described as a SOC-lite service
Agentless Breadcrumb/Bait Deployment
- Breadcrumbs/baits automatically configured and personalized for every individual host
- No footprint left behind on assets. Ensures no additional attack surface and no fingerprints
Securely & Actively Detects Attackers
- Removes the attacker from the network where they can be safely observed and engaged
Deep Visibility
- Provides the attacker’s view
- What’s happening now, not what happened prior
Speedy & Easy Deployment & Management
- Sensors are quickly deployed; projections are almost immediate
Value Pricing
- Pricing is per protected device, not the number of deception elements
How Active Cyber Engagement Turbo-Charges SOC Performance
Detect & Divert Attackers
Lay a minefield of blended traps that confuse, detect, and divert attacks to decoys
Adversary Engagement
Allow the attack to progress in a safe and contained sandbox to observe and collect the attack TTPs
Autonomous Remediation
Use high-fidelity alerts to automatically contain attacks
Investigate & Analyze
Identify compromised systems in the environment with precision and speed
Visibility & Insights
Understand attacker TTPs. Reduce attack surface area. Improve Security posture
Strategic Partnership with Alcalvio
Through a multifaceted partnership for further innovation of Deception technology, Acalvio Cyber Detection Platform works seamlessly with Velaspan’s Active Cyber Engagement service to effectively mitigate security threats.
Connect with us to explore how our active defense approach can transcend your security posture and safeguard your critical business operations.
Let’s Discuss

